AI in Telecom Services
Harness the Power of AI to Build Smarter, More Secure, and Self-Optimizing Telecom Networks
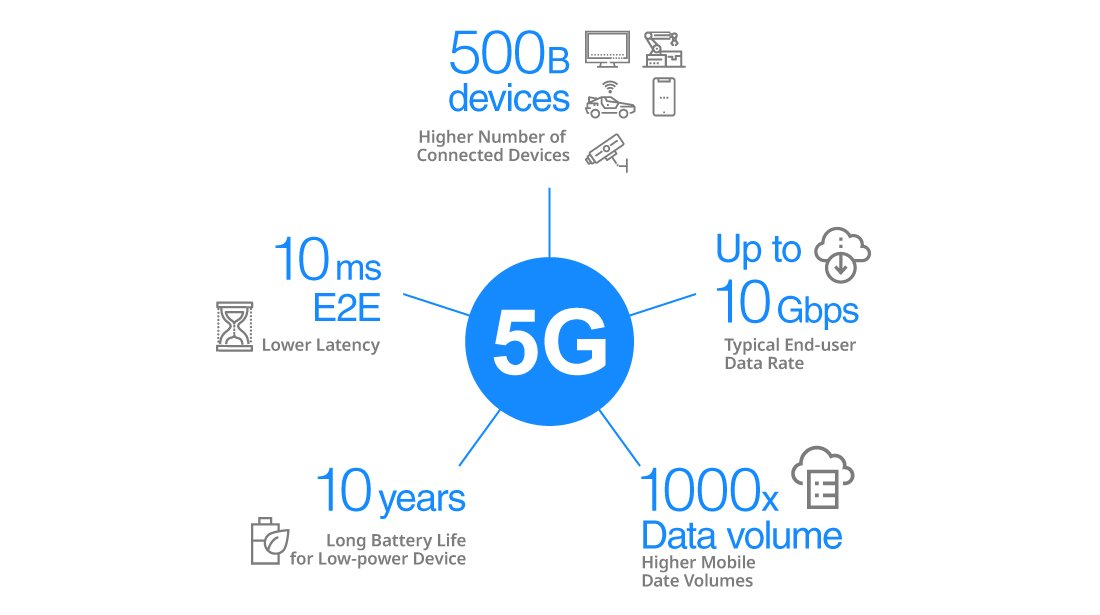
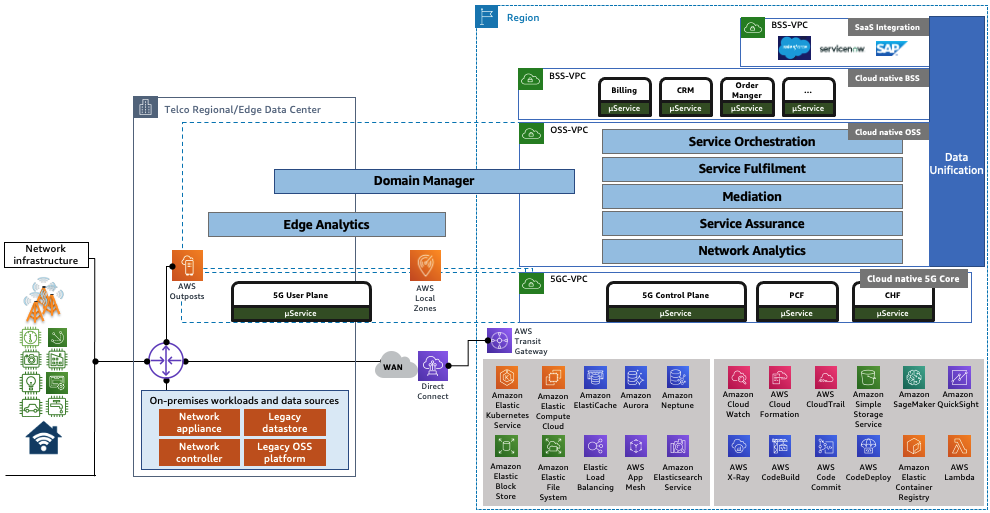
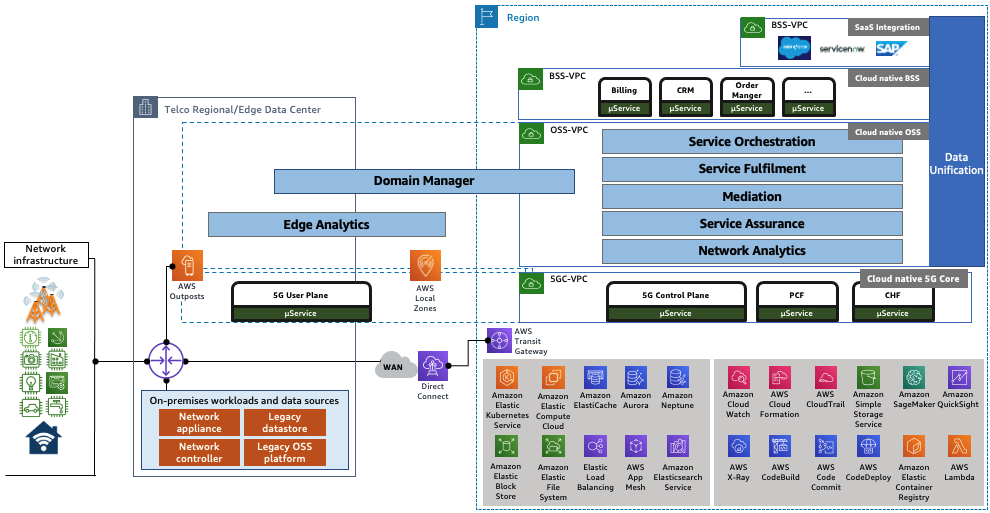
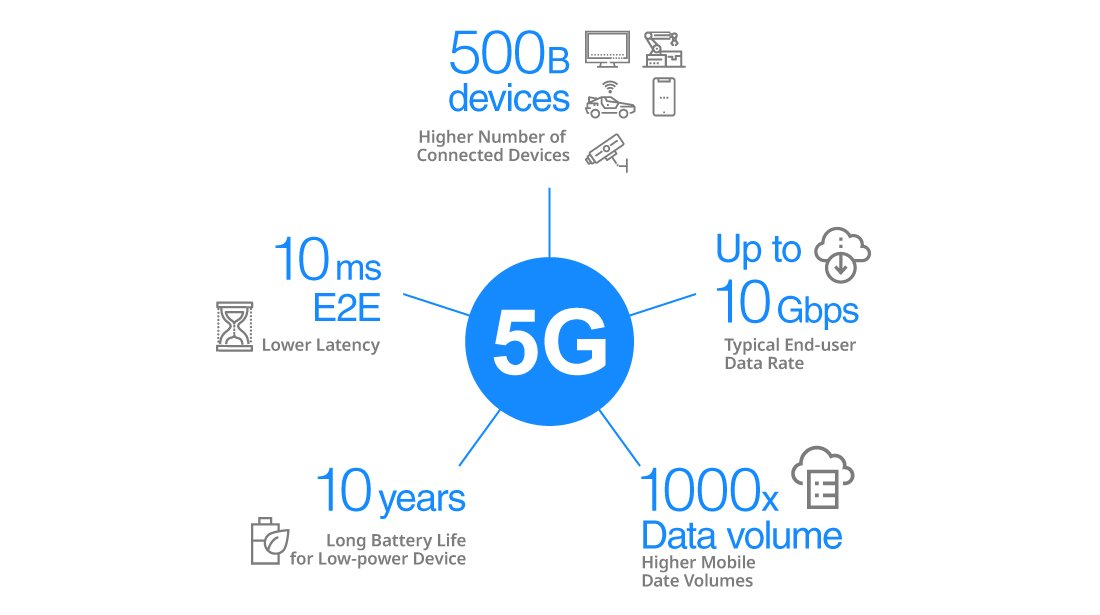
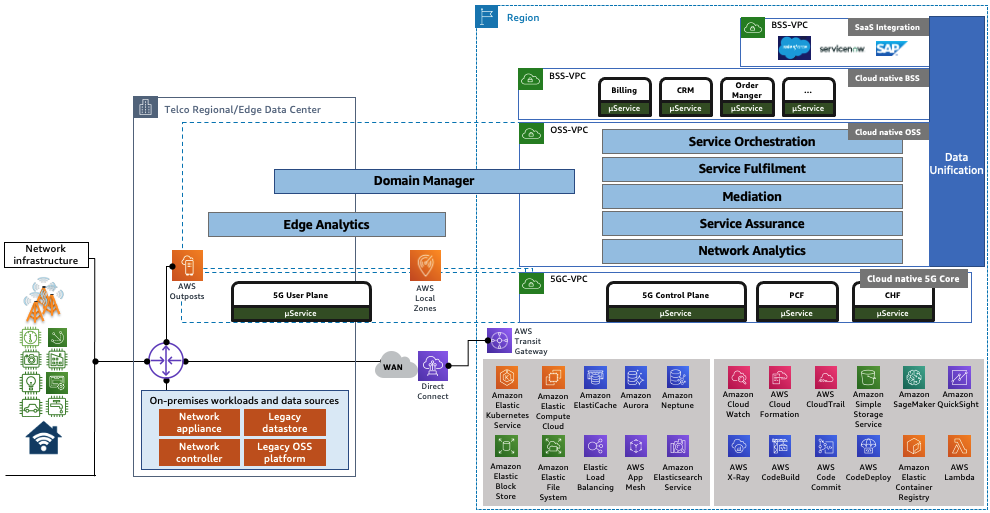
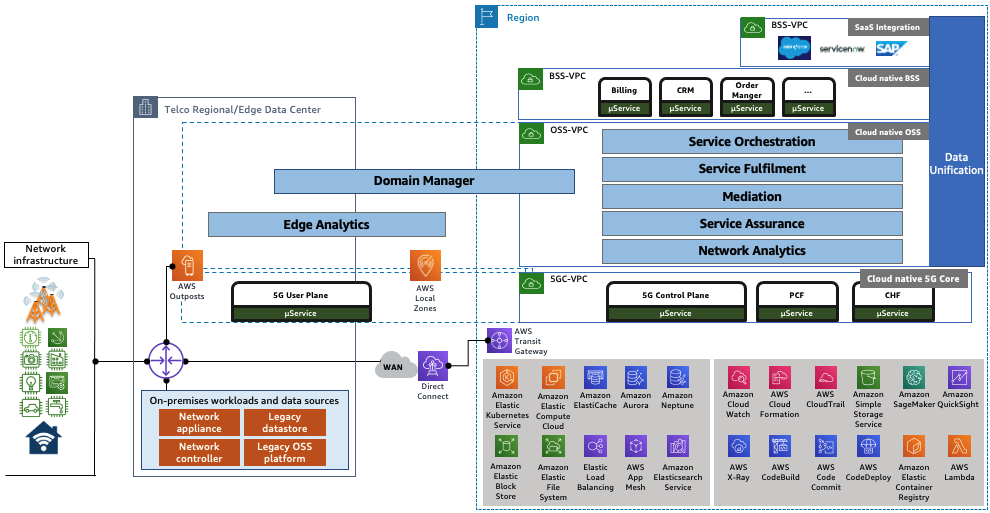
As telecom networks evolve with 5G, ORAN, and edge computing, artificial intelligence is no longer optional — it’s foundational. Our AI in Telecom Services help operators, vendors, and system integrators unlock next-gen capabilities, enabling predictive automation, advanced threat detection, and GenAI-powered decision-making.

AI-Enabled Network Automation & Optimization
Boost performance. Reduce cost. Scale intelligently.
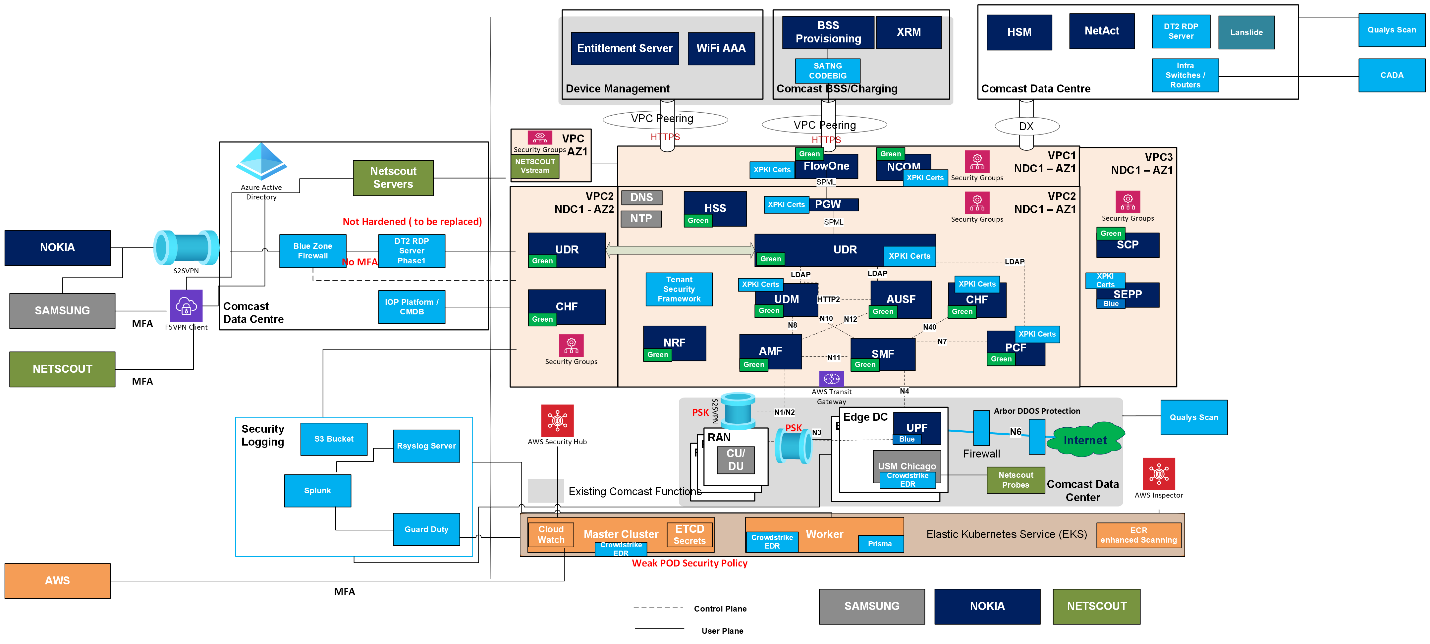
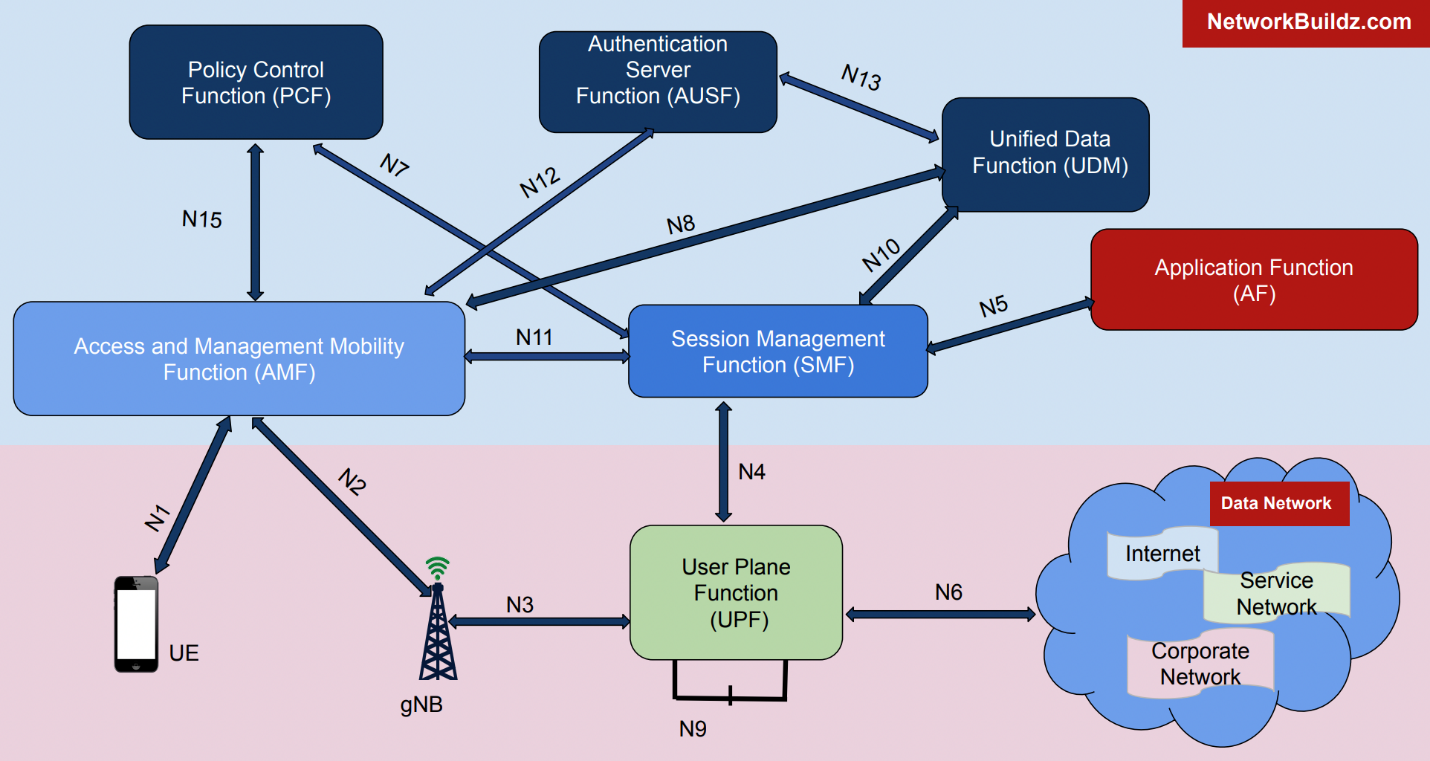
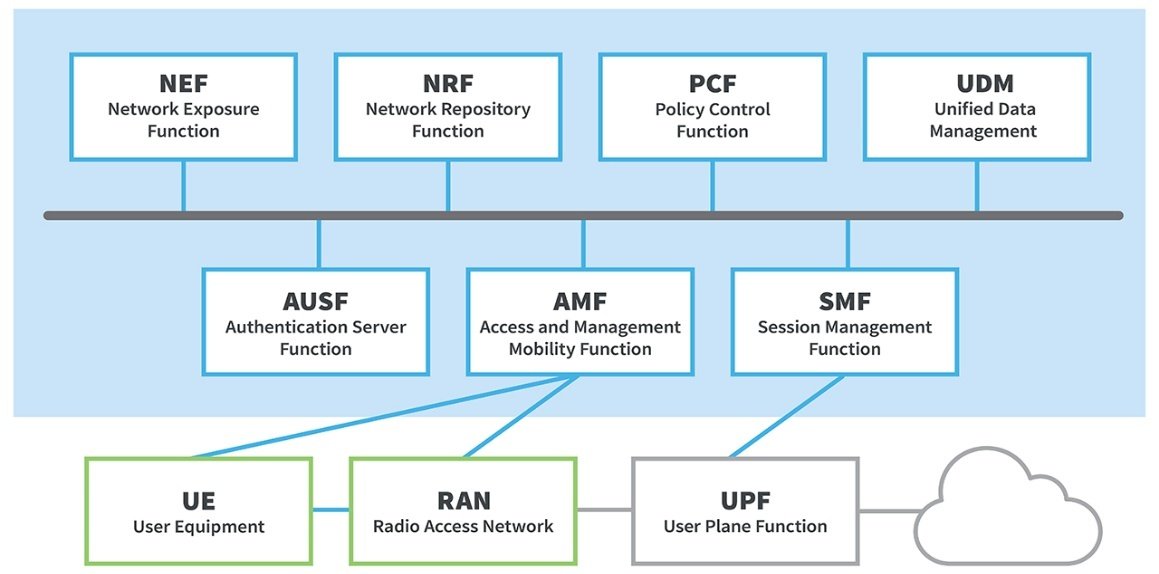
We deploy AI/ML models across the telecom stack to enable dynamic resource allocation, traffic steering, and self-optimization of radio, transport, and core networks. Whether you need pretrained models, fine-tuning, or custom training from scratch, we help you operationalize AI to align with 3GPP and ETSI-defined NWDAF and edge intelligence standards.
Use Cases:
• RAN Self-Optimization (SON), Load Balancing, Cell Outage Detection • Core Network KPI Tuning, NF Scaling, Session Management • AI-driven BSS/OSS Workflow Automation
Methods & Tools:
• ML Pipelines, Reinforcement Learning, Network Slicing Optimization • NWDAF Model Integration, Anomaly Detection, Real-time Inference
Deliverables:
• AI/ML Integration Frameworks • Closed-Loop Automation Playbooks • Model Tuning Reports & NWDAF-Compliant Inference Models
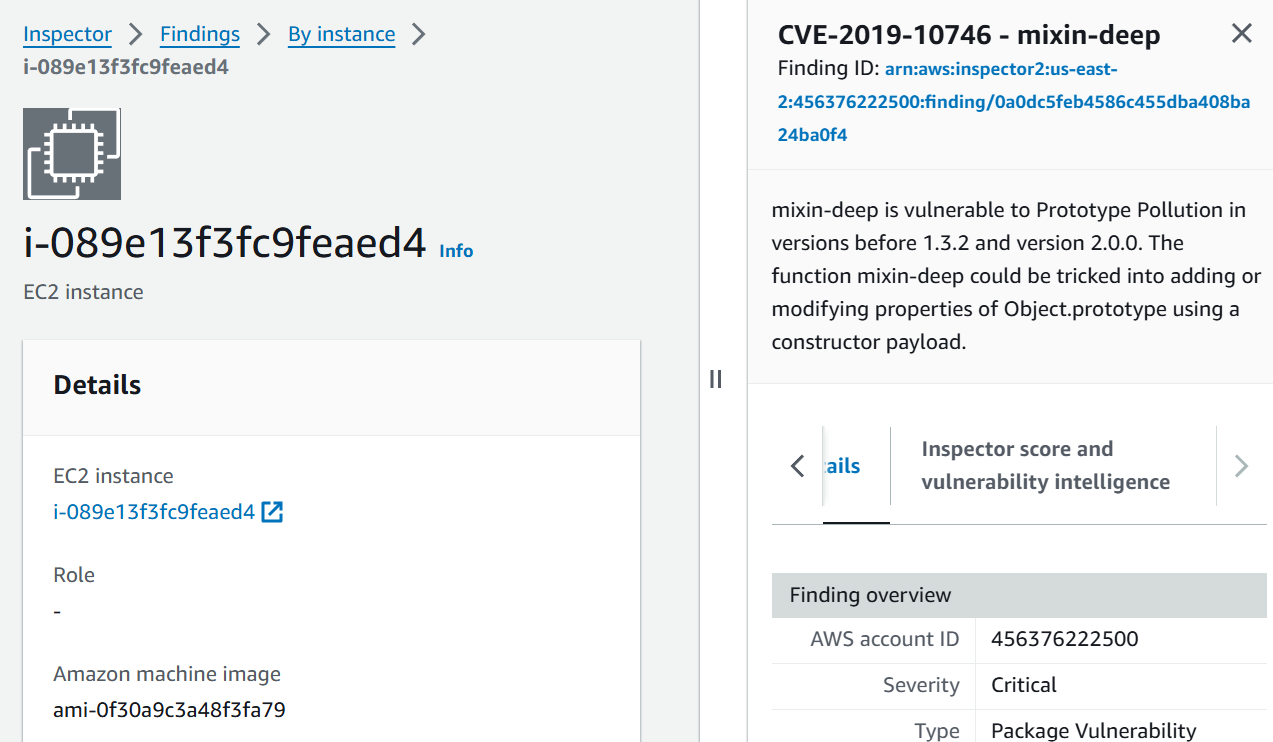
AI-Powered Security & Self-Healing
Secure by design. Intelligence by nature.
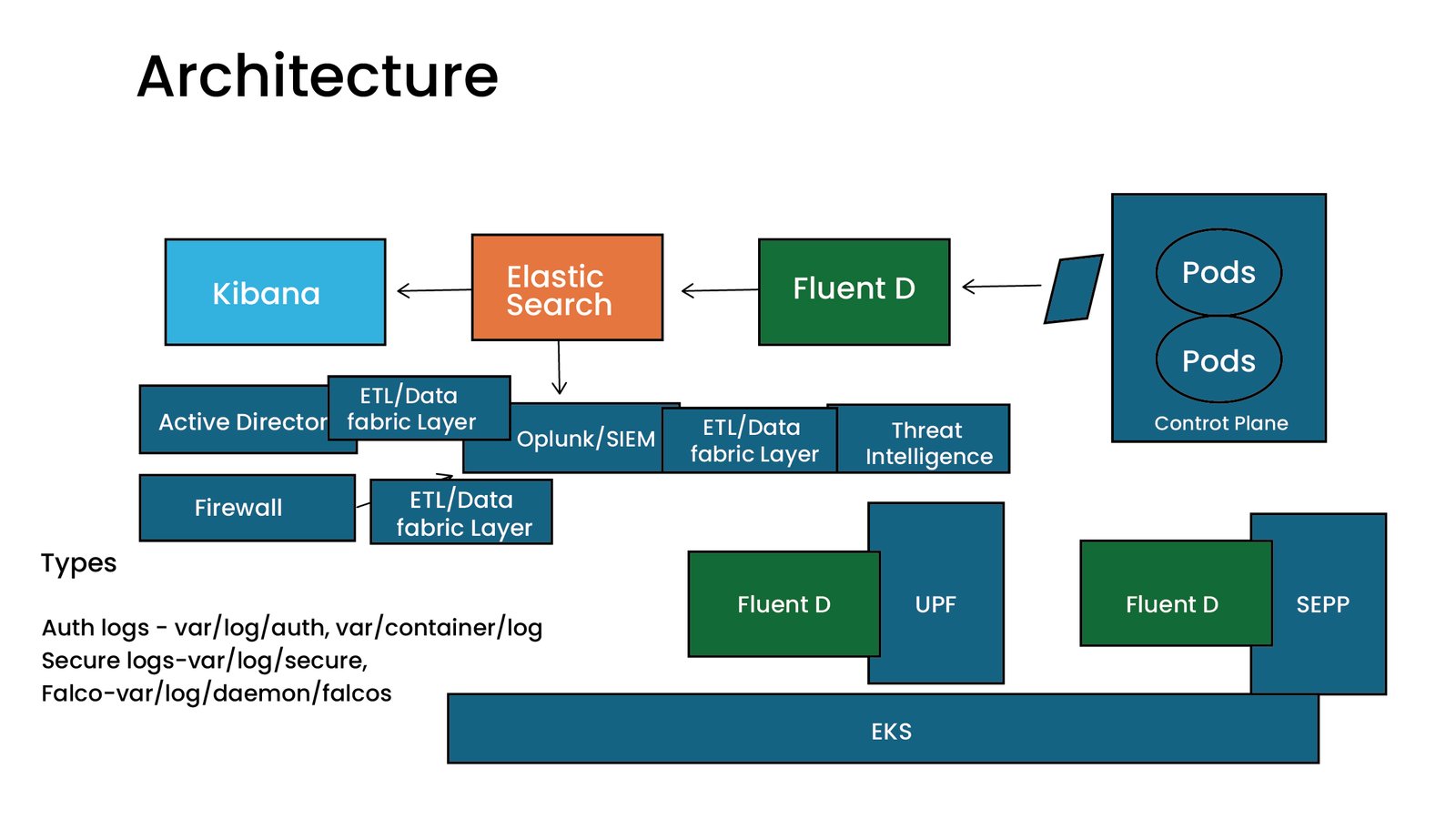
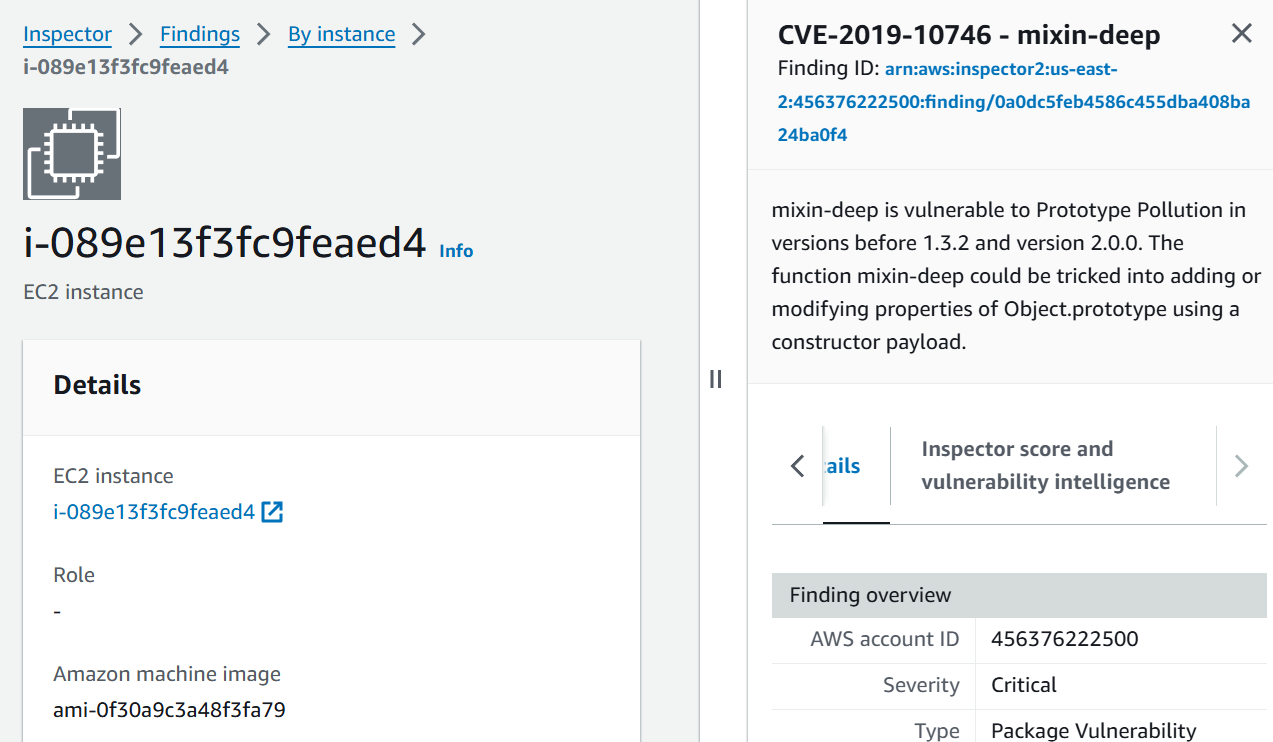
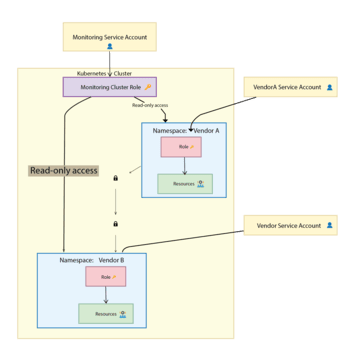
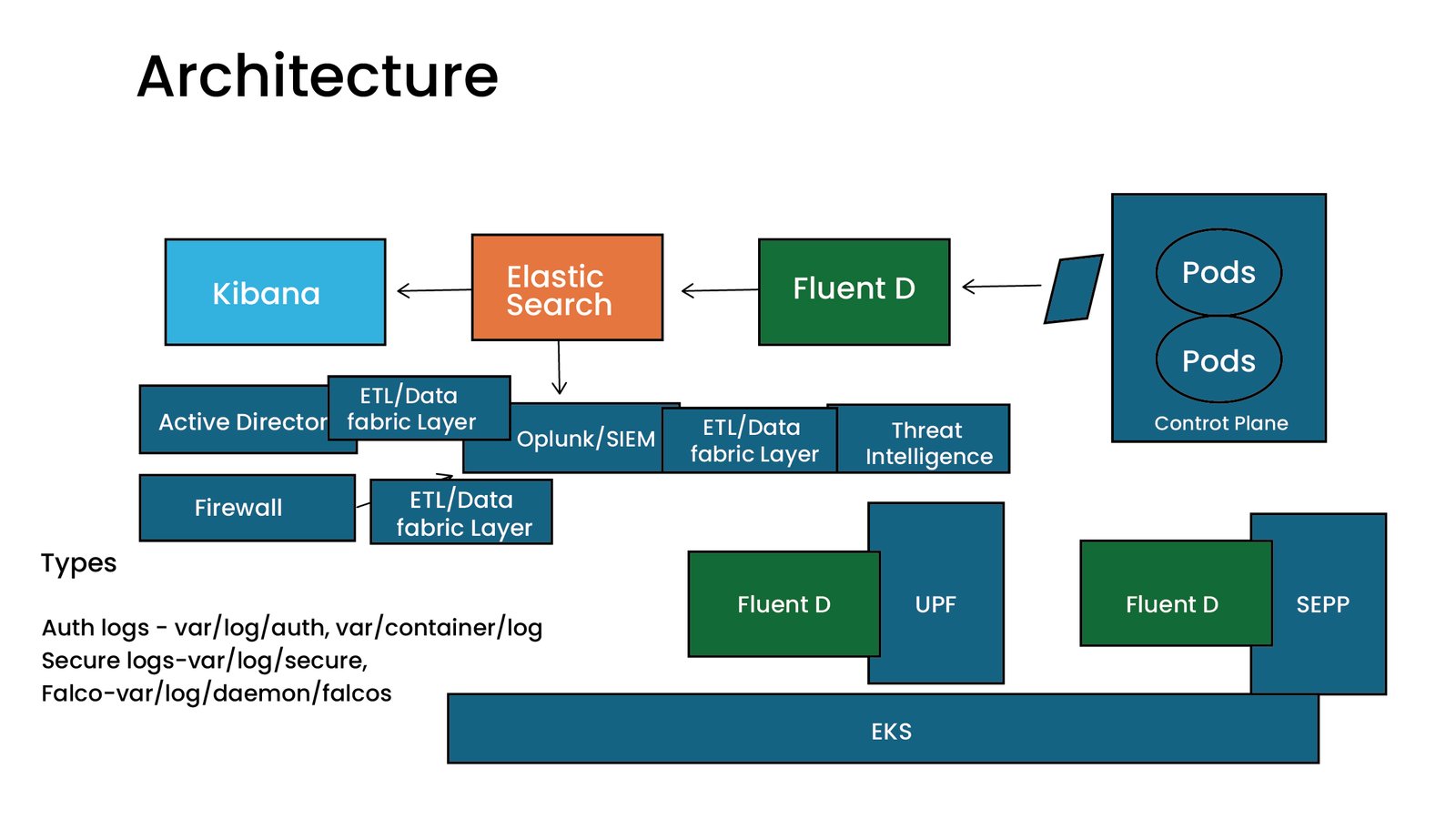
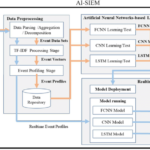
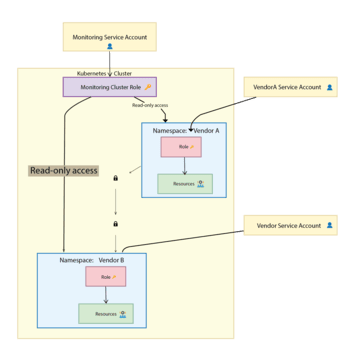
As threats evolve, so must your defenses. We integrate AI and GenAI into your Zero Trust architecture and provide behavioral anomaly detection across users, NFs, and APIs. Our AI models detect threats early, auto-remediate misconfigurations, and support SCAS/NECAS compliance validations.
Use Cases:
• Threat Detection across SBA Interfaces • AI-Driven Orchestration Security • API Abuse Detection, LLM-driven Incident Summarization
Security Tools
•AI-enhanced SIEM/SOAR, Threat Intel Feeds, GenAI-assisted Response
Deliverables:
•Threat Modeling Reports •AI-Based Security Policies •Self-Healing Security Controls (Auto-block, Auto-patch)
AI/ML for Customer Intelligence & Decision Support
Use data as a strategic asset — from the core to the edge.
With AI, operators can elevate customer experience, reduce churn, and anticipate service demand. We help you develop custom LLMs, and NLP models trained on telecom datasets for use in support, personalization, and NOC automation.
Use Cases:
•Predictive Care, Network Issue Summarization, Sentiment Analysis • LLMs for Customer Support Automation (GenAI Chatbots) •Fraud & Usage Anomaly Detection in BSS
Deliverables:
• AI-Driven Insights Dashboards • Telecom-Focused LLM Pipelines • CX Enhancement Playbooks
Course Highlights
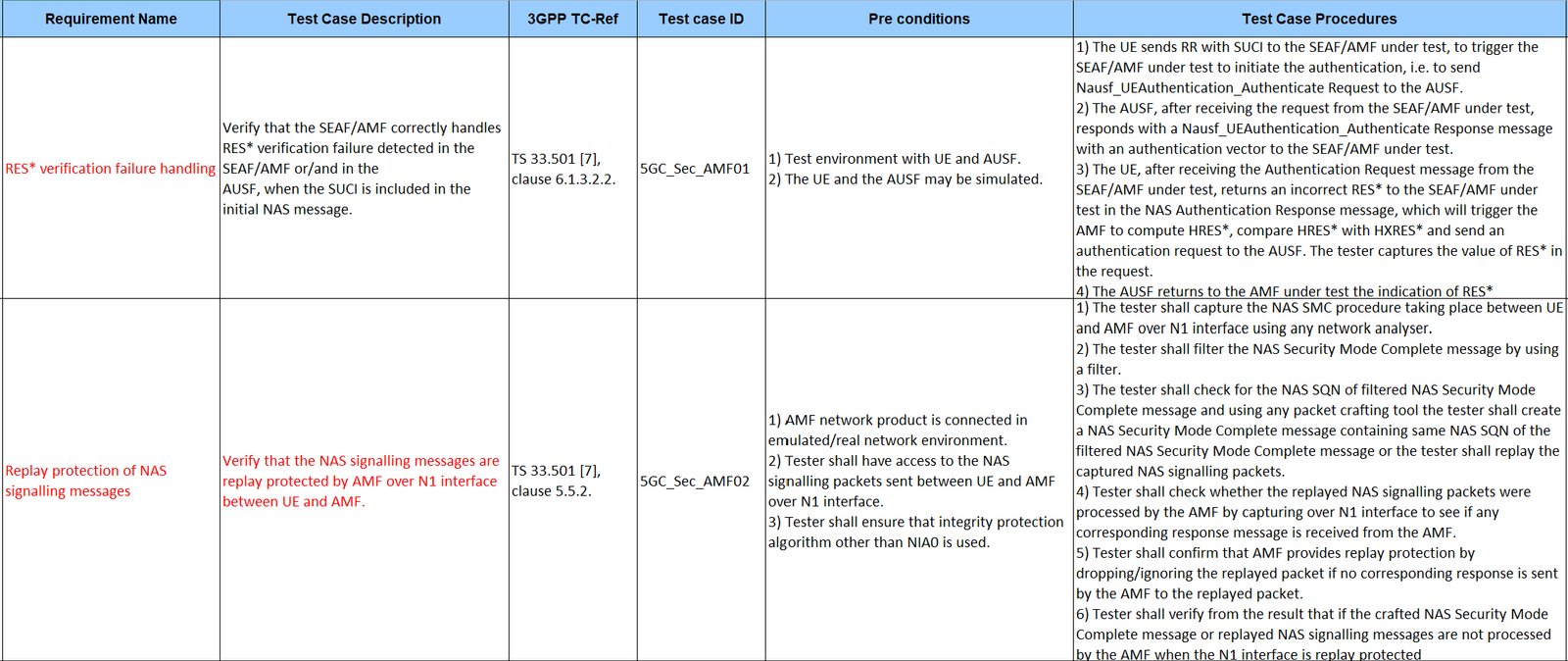
Hands-on Labs
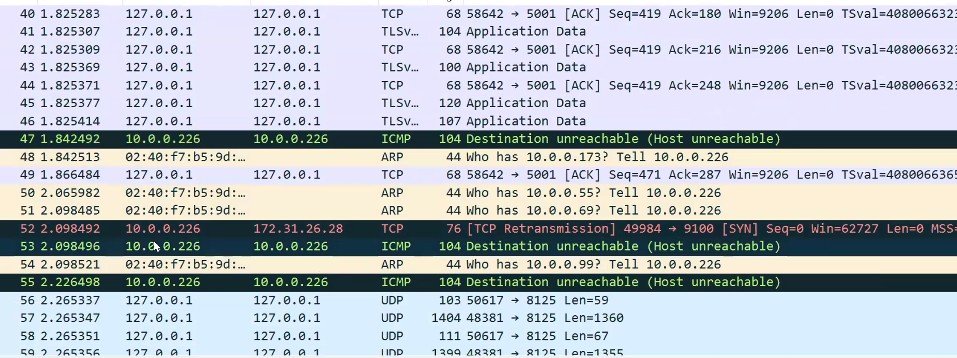
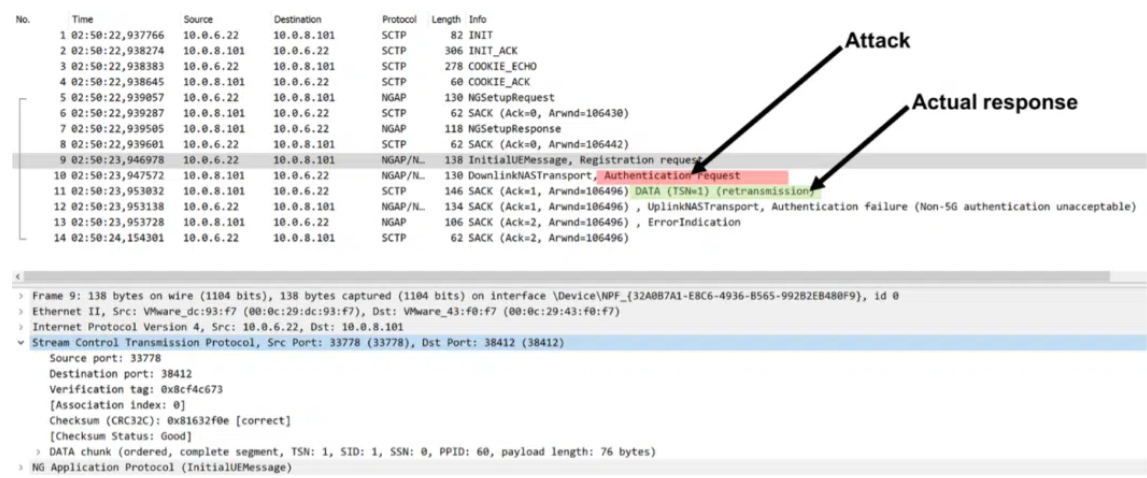
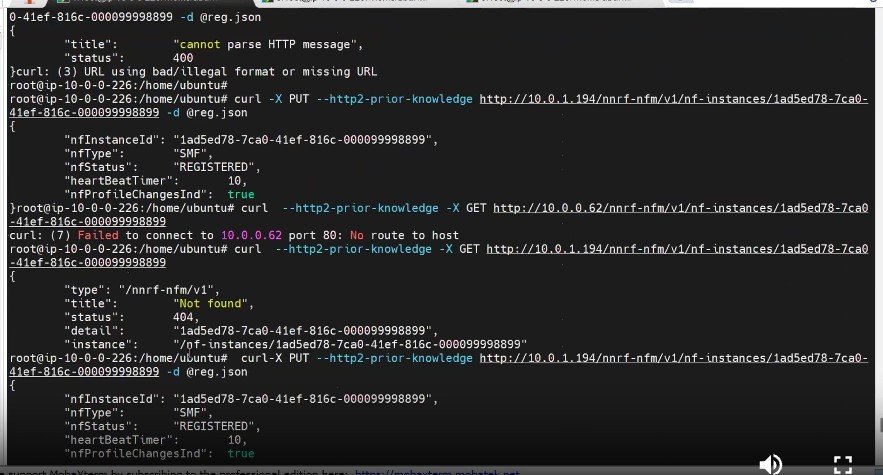
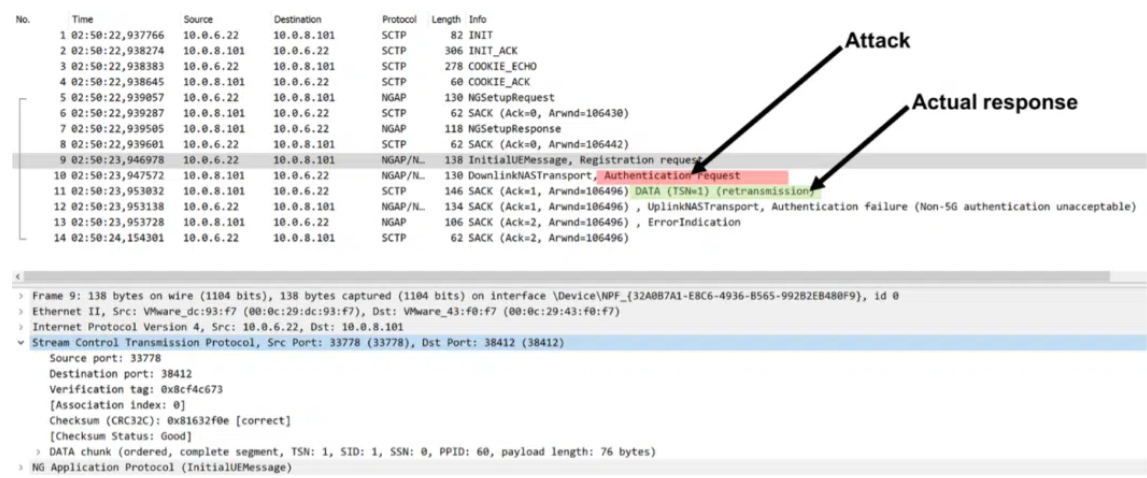
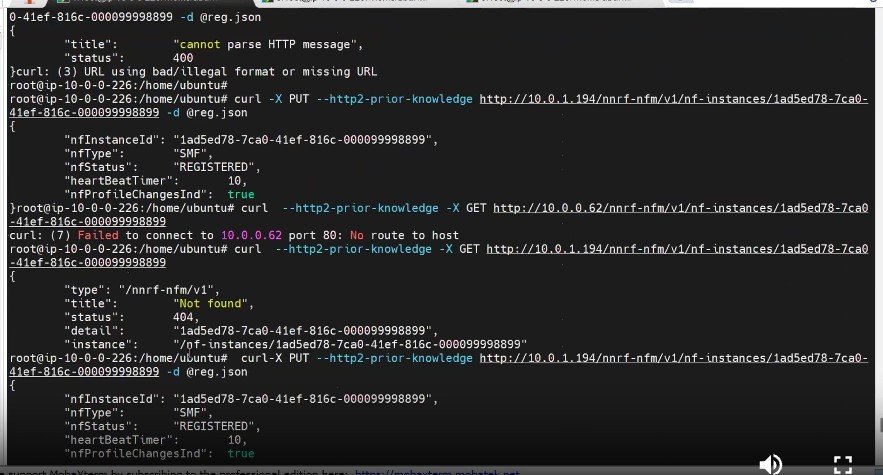
Dive into practical exercises with real-world attack and defense scenarios.
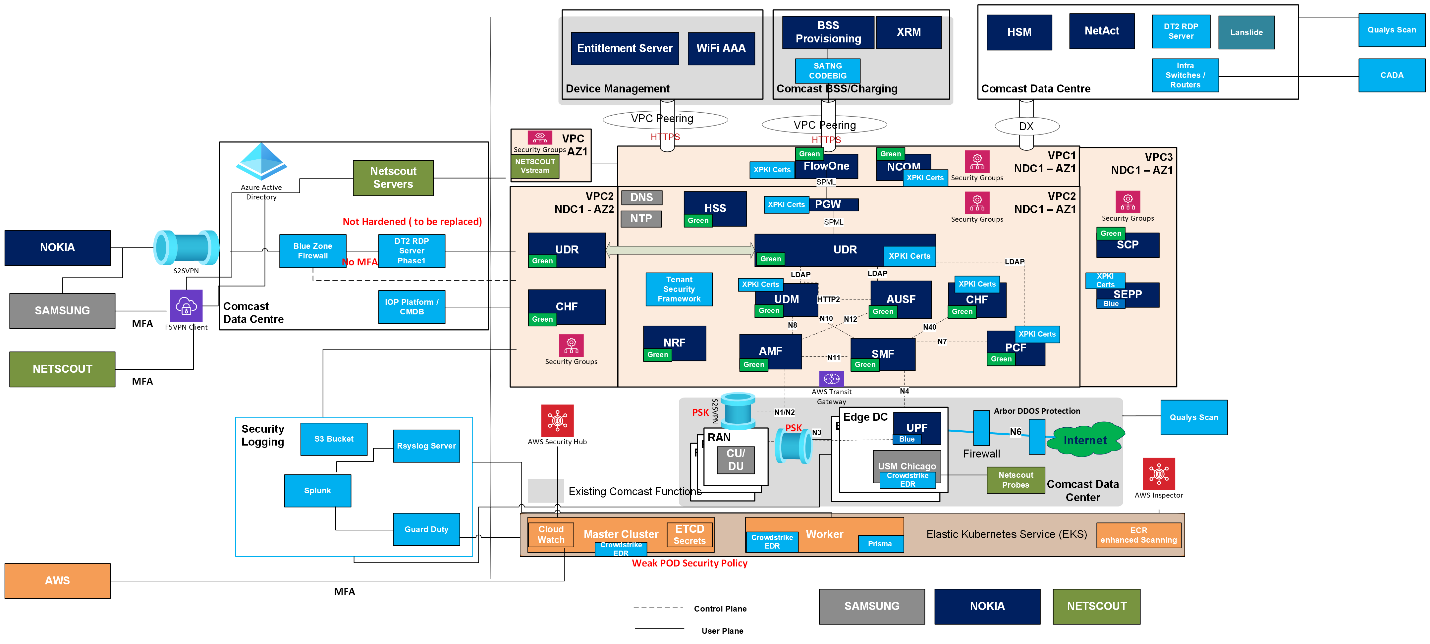
Work on simulated 5G components like Control and User Planes, virtualized Radio, Core, and Cloud NFV stacks deployed in a public cloud environment.
Interactive Sessions
Engage in collaborative discussions and problem-solving exercises.
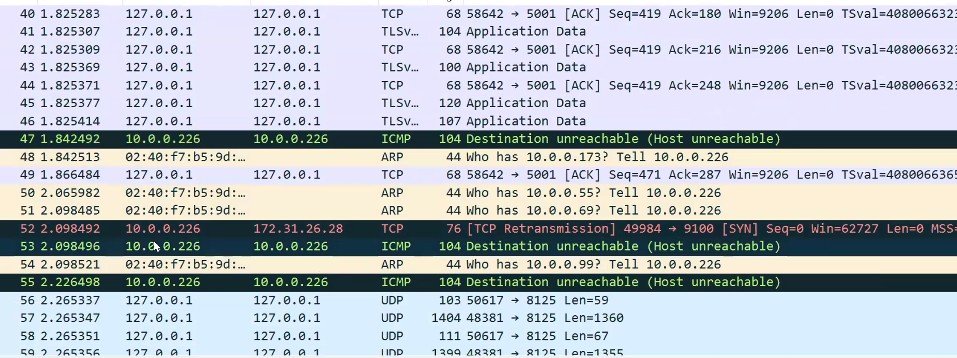
Analyze traces, debug files, and call flows to deepen your understanding of 5G security issues.
Real-World Simulations
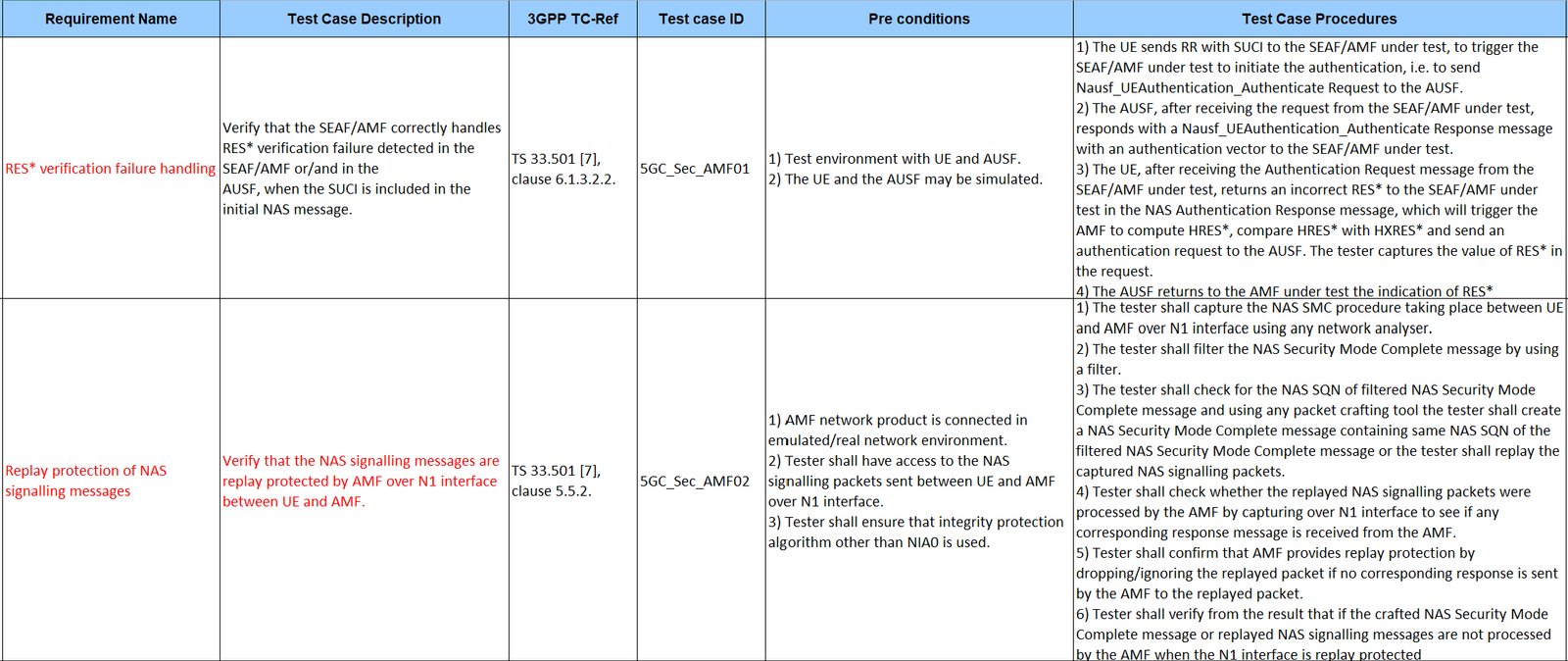
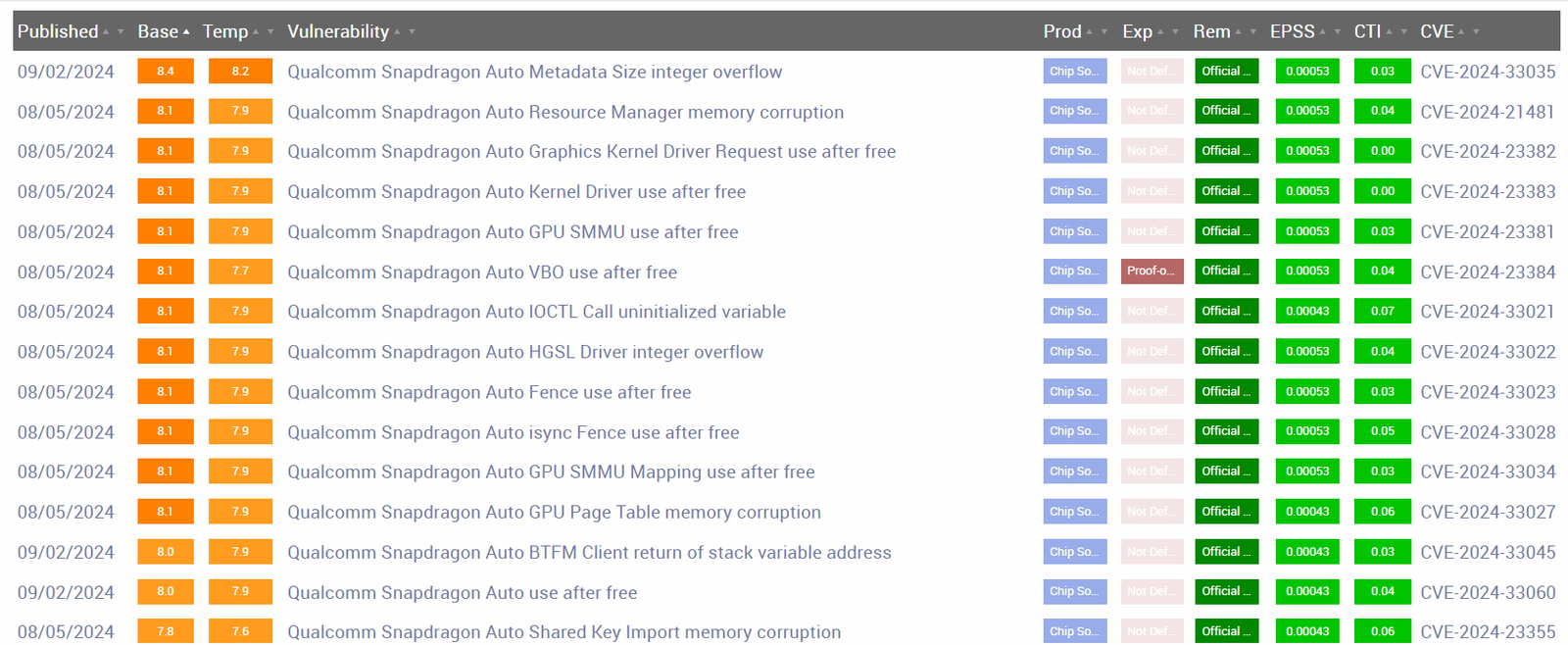
Face simulated 5G network attacks, including SCAS assessments and fuzzing scripts.
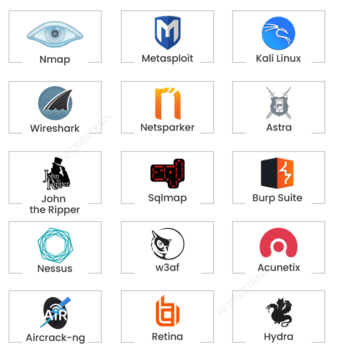
Utilize threat modeling, vulnerability scanning, and penetration testing tools to identify and mitigate risks.
In-Depth Trace Analysis
Master the interpretation of complex attack patterns using tools like Wireshark and Splunk.
Apply MITRE and MOTIF frameworks to trace and analyze sophisticated 5G threats.
Project-Based Learning
Design High-Level and Low-Level Designs (HLDs and LLDs) for enterprise and 3GPP security controls.
Conduct practical security assessments, explore FedRAMP compliance, and build a secure Telecom network as part of your course project.
Case Study Analysis
Examine recent cyberattacks on Tier 1 operators in the US, Middle East, and Asia-Pacific regions.
Perform root cause analysis to understand the tactics, techniques, and vulnerabilities exploited.
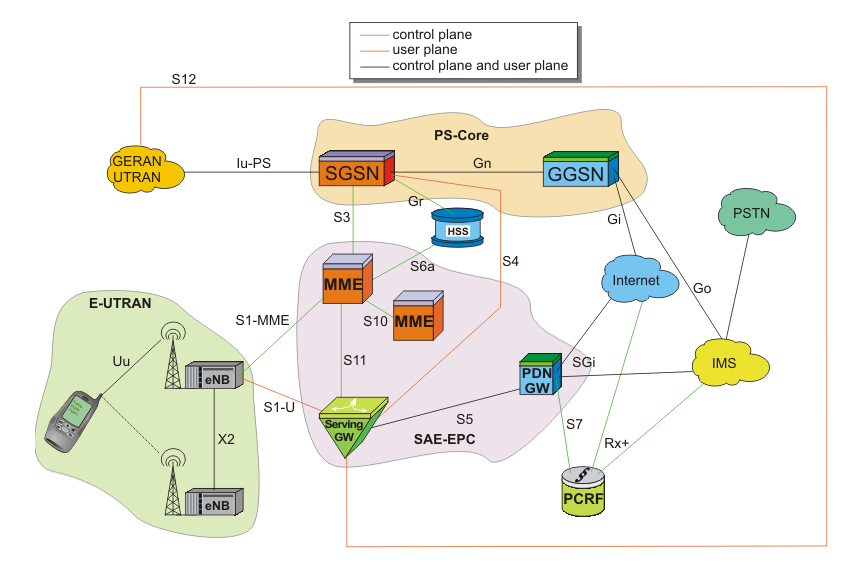
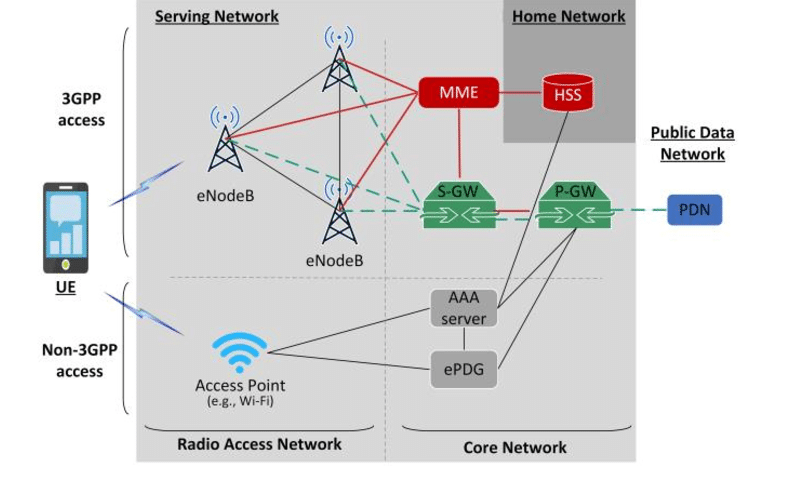
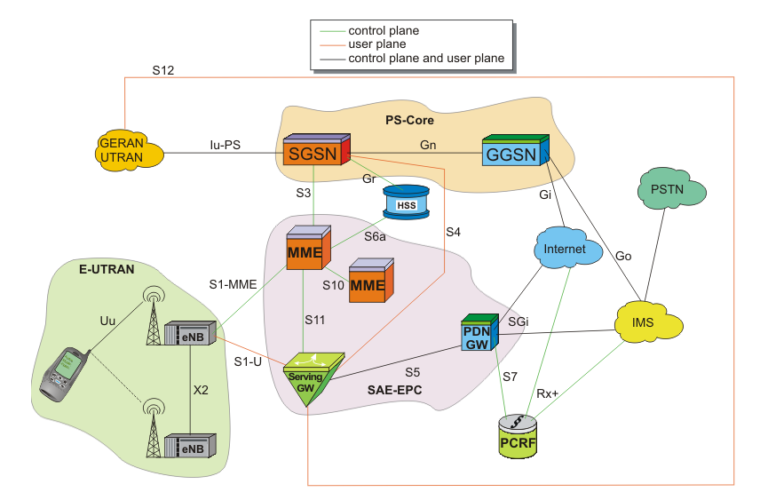
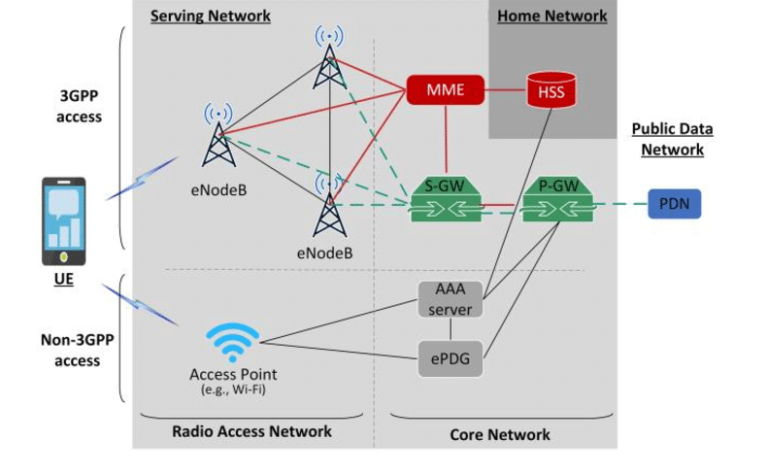
- Start with 4G/LTE Fundamentals
- Progress to 5G Security Concepts
- Master Hands-On Labs
- Explore AI-Powered Use Cases
- Tackle CTF Challenges
- Work on Projects
- Gain Industry Recognition
Start with 4G/LTE Fundamentals
Build a strong foundation in telecom security
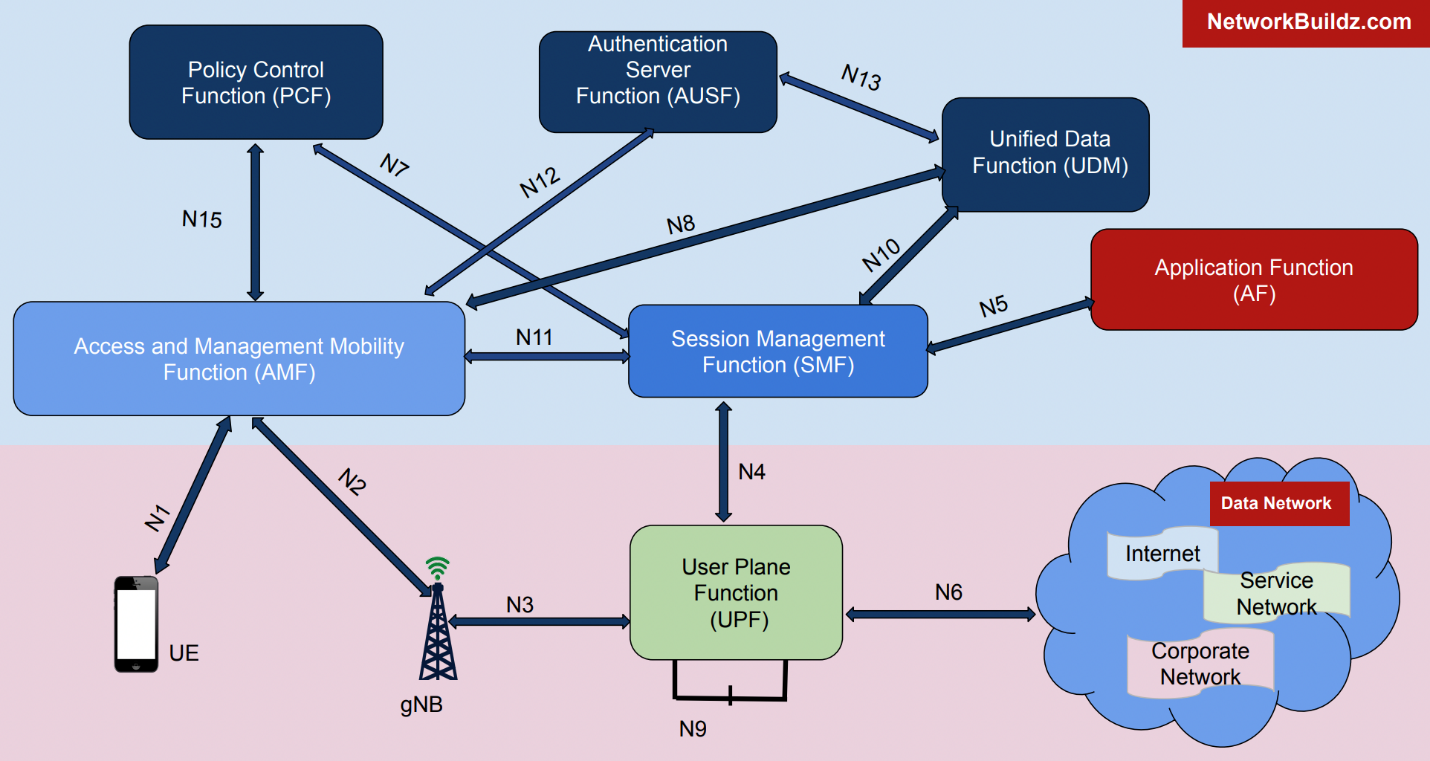
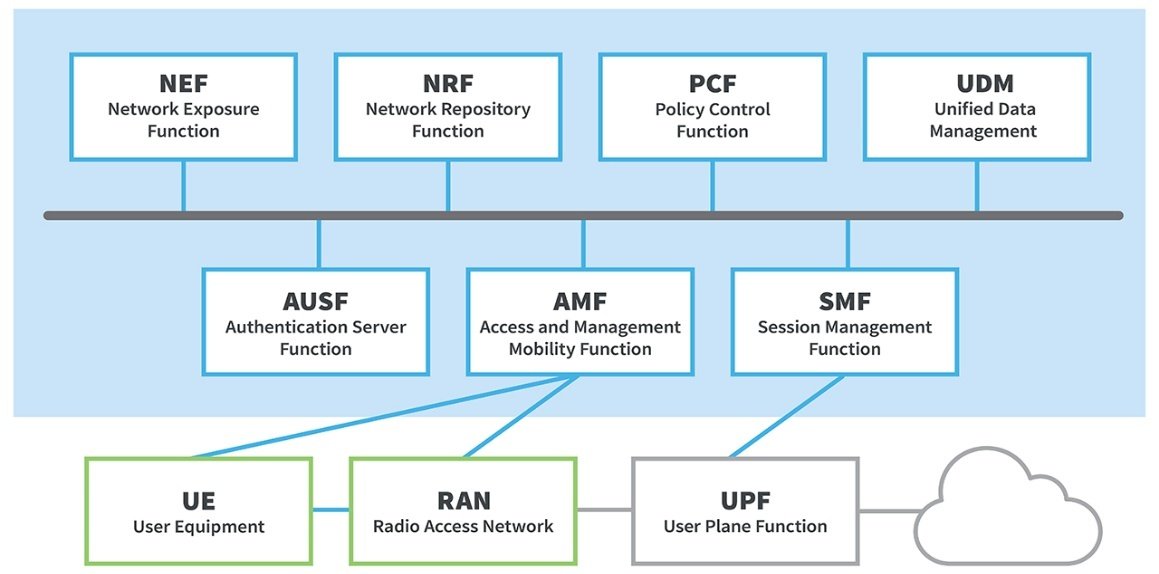
Progress to 5G Security Concepts
Understand architectures and protocols
Master Hands-On Labs
Apply theory to real-world scenarios
Explore AI-Powered Use Cases
Leverage AI in modern security strategies

Tackle CTF Challenges
Test and sharpen your skills in interactive competitions
Work on Projects
Develop and present solutions for advanced use cases.
Gain Industry Recognition
Learn frameworks aligned with 3GPP and ETSI standards.



Start with 4G/LTE Fundamentals
Build a strong foundation in telecom security
Progress to 5G Security Concepts
Understand architectures and protocols
Master Hands-On Labs
Apply theory to real-world scenarios
Explore AI-Powered Use Cases
Leverage AI in modern security strategies








Tackle CTF Challenges
Test and sharpen your skills in interactive competitions
Work on Projects
Develop and present solutions for advanced use cases.
Gain Industry Recognition
Learn frameworks aligned with 3GPP and ETSI standards.




Get Certified and become Job Ready!
Validate your expertise with a recognized certificate.
Success Stories That Inspire
Proven Results That Make an Impact
Your Success Story Starts Here – Register Now
KEY LEARNING OBJECTIVES

Course Highlights
Hands-on Labs
Dive into practical exercises with real-world attack and defense scenarios.
Work on simulated 5G components like Control and User Planes, virtualized Radio, Core, and Cloud NFV stacks deployed in a public cloud environment.
Interactive Sessions
Engage in collaborative discussions and problem-solving exercises.
Analyze traces, debug files, and call flows to deepen your understanding of 5G security issues.
Real-World Simulations
Face simulated 5G network attacks, including SCAS assessments and fuzzing scripts.
Utilize threat modeling, vulnerability scanning, and penetration testing tools to identify and mitigate risks.
In-Depth Trace Analysis
Master the interpretation of complex attack patterns using tools like Wireshark and Splunk.
Apply MITRE and MOTIF frameworks to trace and analyze sophisticated 5G threats.
Project-Based Learning
Design High-Level and Low-Level Designs (HLDs and LLDs) for enterprise and 3GPP security controls.
Conduct practical security assessments, explore FedRAMP compliance, and build a secure Telecom network as part of your course project.
Case Study Analysis
Examine recent cyberattacks on Tier 1 operators in the US, Middle East, and Asia-Pacific regions.
Perform root cause analysis to understand the tactics, techniques, and vulnerabilities exploited.
Benefits of the Bootcamp

Practical, Job-Ready Skills
- Gain hands-on experience with real-world tools, frameworks, and methodologies used in 5G and 4G
- Learn how to assess, secure, and defend Telecom networks, making you indispensable in today’s cybersecurity landscape.

Expert-Led Training
- Learn from seasoned industry professionals with real-world experience
- Get actionable insights and best practices that you can apply immediately in your role.

Stay Ahead of the Curve
- Be at the forefront of securing the next-generation 5G networks.
- Understand cutting-edge attack methods and advanced defense strategies tailored to the unique challenges of 5G.

Build Credibility and Confidence
- Enhance your technical expertise and build confidence in securing complex network infrastructures.
- Develop solutions that align with industry standards, increasing your credibility as a 5G security expert.

Career Growth Opportunities
- Expand your skill set to include in-demand 5G, 4G, Cloud security expertise, positioning yourself for leadership roles.
- Boost your career with knowledge that addresses critical security needs in sectors like telecommunications, IoT, and enterprise IT.
- Demonstrate your project to the telecom and enterprise security leaders.

Network with Like-Minded Professionals
- Connect with other cybersecurity professionals, network engineers, and IT specialists.
- Share ideas, collaborate on projects, and build relationships that extend beyond the bootcamp.
Companies served:




Why 5G Security Matters
Protecting Critical Infrastructure
5G will power essential systems like smart cities, autonomous vehicles, and industrial IoT. Securing these networks is key to safeguarding public safety and ensuring economic stability.
Safeguarding Data Privacy
With 5G enabling faster data transmission and larger-scale collection, protecting user privacy has become more urgent than ever.
Enhancing National Security
Vulnerabilities in 5G networks could jeopardize government communications and critical services, making network security a priority for national defense.
Preventing Economic Losses
A single security breach in a 5G network can lead to massive financial losses and damage trust. Strong security measures are essential for businesses to thrive and innovate.
Addressing Emerging Threats
The unique design of 5G networks creates new vulnerabilities. Staying ahead requires specialized knowledge and proactive strategies to mitigate these risks.
Ensuring Regulatory Compliance
As 5G expands, so do the regulations governing its security. Organizations must adopt compliant security measures to avoid penalties and maintain operational continuity.
Why Partner with Us?

- AI Built for Telecom – Not generic ML, but telco-native AI aligned with real-world 5G/ORAN/BSS use cases
- From Lab to Production – End-to-end support from model training, optimization, and MLOps deployment
- Standards-Compliant – We speak 3GPP, ETSI, ORAN, and GSMA — and design accordingly
- Security-First GenAI – We embed trust, guardrails, and compliance in every LLM or AI workflow
Frequently Asked Questions (FAQs)
Once enrolled, you’ll receive access to our Learning Management System (LMS) using your registered ID. Through the LMS, you can join live sessions, access course materials, and stay updated throughout the bootcamp.
Yes, all sessions will be recorded, and you’ll have access to the recordings after the bootcamp concludes.
Unfortunately, refunds are not available. However, we are committed to your learning journey and will collect feedback after each class to address any concerns and ensure that your learning objectives are met.
You will have access to the lab environment for a total of 2 weeks: 1 week during the bootcamp and an additional week afterward to complete assignments and resolve any remaining doubts.
Yes, an orientation class will be scheduled, and you’ll receive an email with the details. This 1-hour session will provide your credentials, guide you through the lab setup, and address any technical issues to ensure a smooth start.
Each class begins at 13:00 EST and follows this structure:
- Lecture: 1.5 hours of in-depth learning.
- Quiz: A short quiz to reinforce key concepts.
- Break: 15-minute break for refreshment.
- Lab: 1 hour of hands-on practice in the lab environment.
- Q&A and Feedback: 10-15 minutes to address questions and gather feedback at the end.
You will receive your certificate by the end of Day 5 of the bootcamp.
All bootcamp assignments and project work must be submitted through the Learning Management System (LMS).
You can contact our support team by emailing support@xecuritypulse.com, and we’ll respond within 24 hours.
Testimonials
Let’s Build Your AI-Ready Network
Contact us to schedule an AI Strategy Workshop or Demo.
